Many homes today have a wireless router in their home. This constant connectivity to the internet allows them to have continuous access to the wider network. They can communicate on social media, access videos, and TV shows, play games online, and much more. Wireless routers can also be a security risk when they’re unsecured. Through wireless routers, hackers can access personal information and even devices without the homeowner ever suspecting a thing.
How Does a Wireless Network Work?
Many people have at one point or another come into contact with a wireless network. While how they work is not really a secret, many people still don’t understand the intricacies behind them. Wireless routers help people connect to the internet by being an access point, like a DSL modem or a cable, that connects to the router. The router sends the signal into the air and in many cases can reach up to a few hundred feet.
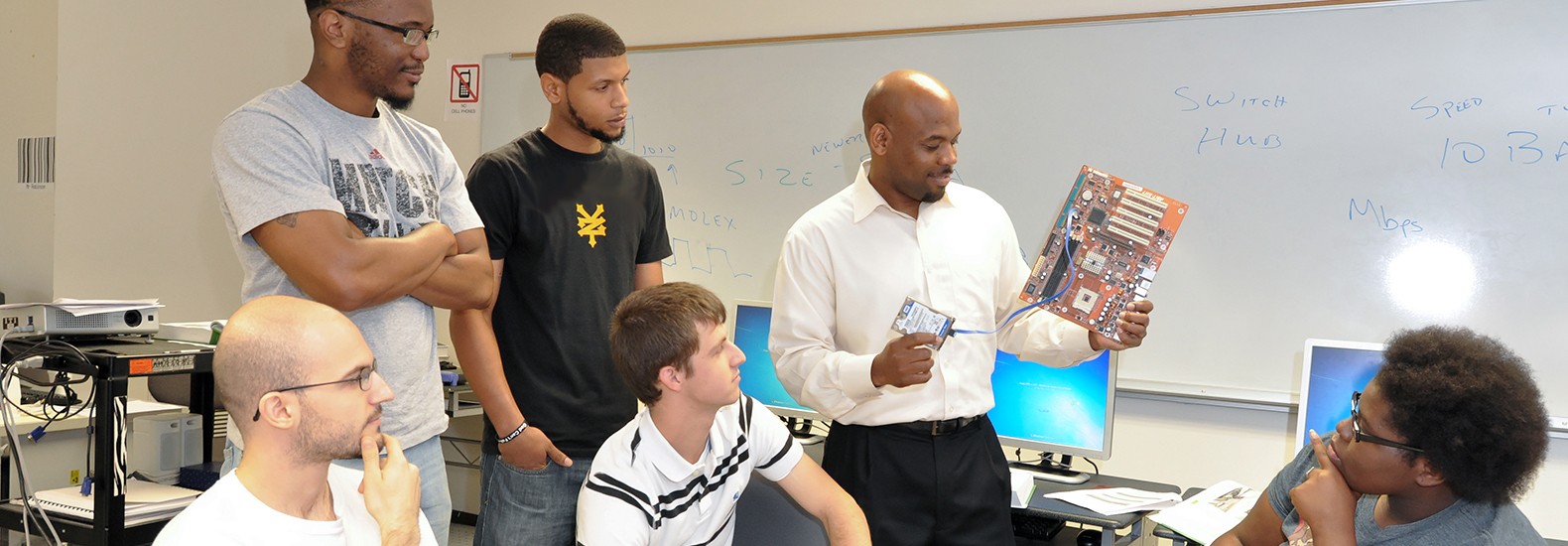
People interested in an information technology security career will know an unsecured wireless network is vulnerable. Anyone can access these unsecured networks to access information from a person’s device. There have been cases where unsavory individuals have committed a crime or sent span through an unsecured network of an unsuspecting person. The criminal activity is then traced back to the account of the person with the unsecured network.
Encryption Can Help Protect Your Router, Computer, and Other Devices
Anyone with an information security degree knows that the first step to securing a router is to encrypt the information being sent over the wireless network. This encryption prevents attackers from eavesdropping on the communications taking place over the network. Encryption basically scrambles up the information into a code that cannot be accessed by other people. Using this form of protection is one of the most effective ways to secure a network from hackers.
There are two main types of encryption people will use to secure their network. The first is Wi-Fi Protected Access (WPA) and there is the second one which is Wired Equivalent Privacy (WEP). The router, computer, and other devices will use the same encryption that is set on the wireless network. The WPA2 is considered the strongest encryption protection for a wireless network. WPA2 can protect people from the majority of hackers.
Older routers may use WEP encryption, but won’t be strong protection against some of the more sophisticated hacking programs. People with older routers are usually recommended to upgrade to a new one with WPA2 capability to secure their wireless network.
The majority of wireless routers will come with the encryption feature switched off. People have to turn it on and follow the directions to set up the router. Many routers usually come with a manual on how to set them up or people can find directions on the company’s website.
Limiting Access to a Network
 One of the first things people seeking an information security degree learn is securing and limiting access to a wireless network. Limiting access to a network is another way to protect it from being hacked by intruders. Allowing only certain devices to access the wireless network helps to keep it more secure. Devices that are able to access the wireless network will be assigned a Media Access Control (MAC) address that is unique to the device. Wireless routers will normally have a mechanism to allow certain devices with a certain MAC address access to the network. There are a couple of hackers who can mimic a MAC address to fool the network, so relying on this security measure alone is no guarantee of complete safety.
One of the first things people seeking an information security degree learn is securing and limiting access to a wireless network. Limiting access to a network is another way to protect it from being hacked by intruders. Allowing only certain devices to access the wireless network helps to keep it more secure. Devices that are able to access the wireless network will be assigned a Media Access Control (MAC) address that is unique to the device. Wireless routers will normally have a mechanism to allow certain devices with a certain MAC address access to the network. There are a couple of hackers who can mimic a MAC address to fool the network, so relying on this security measure alone is no guarantee of complete safety.
Securing the network of a wireless router is much easier than people think. One of the downsides is that many people often overlook securing their network in the first place which leaves it open to hackers. Securing these wireless networks ensures hackers are unable to access them and can prevent them from committing crimes over an unsecured network.
For more information about graduation rates, the median debt of students who completed the program, and other important information, please visit our website: https://iticollege.edu/disclosures/