After you earn an Associate of Occupational Studies (AOS) Degree in Information Technology, you may find yourself dealing with internet technology security in a position of authority. If so, you will need to make sure that you’re running the department correctly. So, with that being the case, what security essentials does the business need? How can you go about making sure that it runs smoothly? Today we’re going to go over a few crucial points that you need to consider when you are running any sort of information technology department, especially if you control the security.
Step 1: Have a Clear Plan
We cannot say this enough: as an information technology security officer you need to make sure that you have a clear plan in place. The plan will need to reflect the following:
Company Priorities – What does the company value? What should you be focusing on? Customer information? Finances? Employee information? Infrastructure?
Institutional Capabilities – You probably have a lot of things that you would like to be doing but here’s the big question: what is the company capable of doing? You don’t want to plan any measures that you cannot enforce, and with that being the case, it would be a good idea to make sure that you’re taking the company’s resources into account when you make plans.
Latest Best Practices – This is an interesting part of the process because it requires you to do far more than just make plans. You need to be versatile in keeping up with the latest technologies and the latest best practices. Doing so will make your defense more effective and your company will run better.
Step 2: Keep your Cyber Security Measures Up to Date
Do you know how often things change in the cybersecurity industry? Twice a day if we’re being honest, but from a realistic standpoint, you should be constantly evaluating your company’s security measures. Assess the risk in terms of security measures, look at liability, and explore the potential for a breach of sensitive information. You can create your own custom solutions, draft internal policies, and ensure that your measures are effective. Internal policies can include:
* Protection Against Breach of Sensitive Information
* Mobile Device Security/Management
* SIEM/SSL Security Layers
* Firewalls
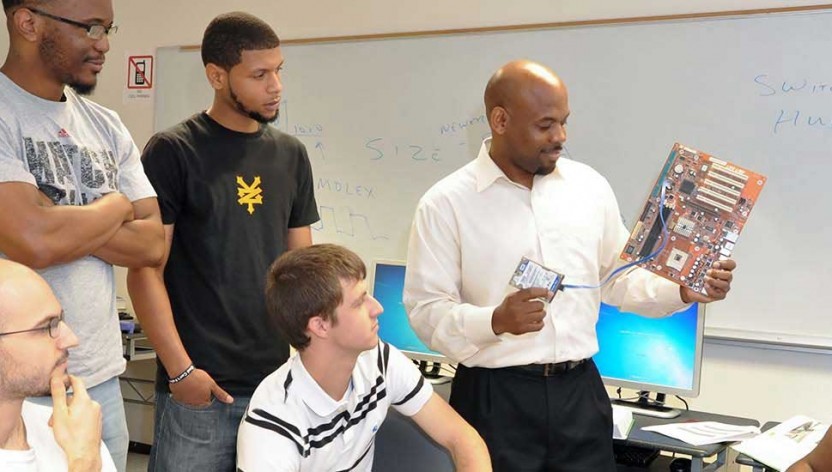
Step 3: Train Your Staff
One of the most important things that you can do is keep your staff trained. You can have as many contingency plans as you want, but if your staff isn’t properly trained then it’s all going to be for nothing; seriously. Keep them up to date on the company policies, plans, and procedures, and most importantly, make sure that they’re updated on industry standards. You could go for months without a single breach, but when a breach occurs, you’re going to want to be ready without exception.
Step 4: Make a Backup
It may not be today, and it may not be next week but eventually, your data is going to be compromised and you want to be there to take care of it when it does happen. A strong backup is a lifeboat, to put it as simply as possible. In information technology security school, you will learn all about the art of making redundant backups, ensuring that the company information is perfectly safe.
These four steps will help you to create a more secure workplace and you are going to need them as an information security officer. Call us today to get information on our programs, and to get started with your career.
Disclosure:
For more information about graduation rates, the median debt of students who completed the program, and other important information, please visit our website: https://iticollege.edu/disclosures/