We are quickly moving past the need for physical passwords and we’ve seen everything from fingerprint readers all the way to voice print authorization. On September 12th, 2016, Apple introduced the replacement TouchID, known as Face ID. The name is self-explanatory but how does it work and is it actually practical? While pursuing your information security degree you are going to learn that Face ID is powered by the TrueDepth camera which is able to project and analyze over 30k points on the human face. Through this it creates a precise and accurate depth map of your phase, ensuring that it recognizes you and only you as you sit down at the computer. In theory, this should make your computer more secure than ever before.
How it Works
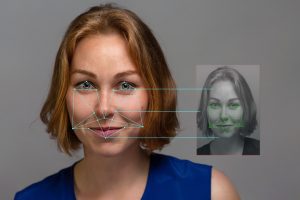 We’ve already covered the points and face mapping, but what we haven’t touched yet is potential for spoofing. One of the biggest questions that we and many other people tend to have about this technology is whether or not it’s actually going to be able to prevent spoofing. While it seems unlikely for the average user there is a small chance that a would-be hacker might attempt to physically circumvent this security by using a mask or photo. The facial map it takes from you initially will be encrypted and it is protected by the Secure Enclave. Furthermore, the authentication is not cloud-based; it is device based meaning there is no chance that the image will have been swapped.
We’ve already covered the points and face mapping, but what we haven’t touched yet is potential for spoofing. One of the biggest questions that we and many other people tend to have about this technology is whether or not it’s actually going to be able to prevent spoofing. While it seems unlikely for the average user there is a small chance that a would-be hacker might attempt to physically circumvent this security by using a mask or photo. The facial map it takes from you initially will be encrypted and it is protected by the Secure Enclave. Furthermore, the authentication is not cloud-based; it is device based meaning there is no chance that the image will have been swapped.
Changes in Your Appearance
Another concern is that potential users have the possibility of changing their appearance over time. You could grow a beard, wear a hat, or even go overboard on your makeup. Face ID, however, is powered by the A11 Bionic Chip which should allow for variations in appearance. Theoretically, it could learn your appearance and see through any changes that have been made.
Speed is Everything
 Lots of people hate entering a password every single time they want to use their device, phones included, and with that being the case fingerprint and face identification became a matter of natural profession for the brand. Early data indicated that while the iPhone was quickly becoming an integral part of everyday life for many people, the majority of people were not using passcodes even on the lock screen because it was simply too slow and too inconvenient. When it comes to accessing your phone, speed is absolutely paramount and the introduction of facial recognition will help to bring about a better method of access.
Lots of people hate entering a password every single time they want to use their device, phones included, and with that being the case fingerprint and face identification became a matter of natural profession for the brand. Early data indicated that while the iPhone was quickly becoming an integral part of everyday life for many people, the majority of people were not using passcodes even on the lock screen because it was simply too slow and too inconvenient. When it comes to accessing your phone, speed is absolutely paramount and the introduction of facial recognition will help to bring about a better method of access.
Increasing Security
 While it is certainly the user’s prerogative to not use a passcode, it does create a bit of a security problem. One of the things that we’ve brought attention to as of late is the security breaches that can occur with mobile devices and a lack of a passcode doesn’t help. While your phone might be protected from remote breaches, it is difficult to protect it from physical breaches. i.e, a person physically takes your phone and begins to sort through the data within. While we might change intellectually over the years, our faces remain almost exactly the same.
While it is certainly the user’s prerogative to not use a passcode, it does create a bit of a security problem. One of the things that we’ve brought attention to as of late is the security breaches that can occur with mobile devices and a lack of a passcode doesn’t help. While your phone might be protected from remote breaches, it is difficult to protect it from physical breaches. i.e, a person physically takes your phone and begins to sort through the data within. While we might change intellectually over the years, our faces remain almost exactly the same.
The face is the perfect highly consistent ID and while this new technology from Apple is bound to have a few hiccups here and there, overall most are pretty confident that the new technology will work very smoothly and that it will help to streamline security in ways that we’ve never seen. As part of your information technology security training, you will become intimately familiar with it as it becomes more and more widespread. This is just a small portion of your new career and a small part of what you will be learning at our facility. Contact us for more information.
For more information about graduation rates, the median debt of students who completed the program, and other important information, please visit our website: https://iticollege.edu/disclosures/