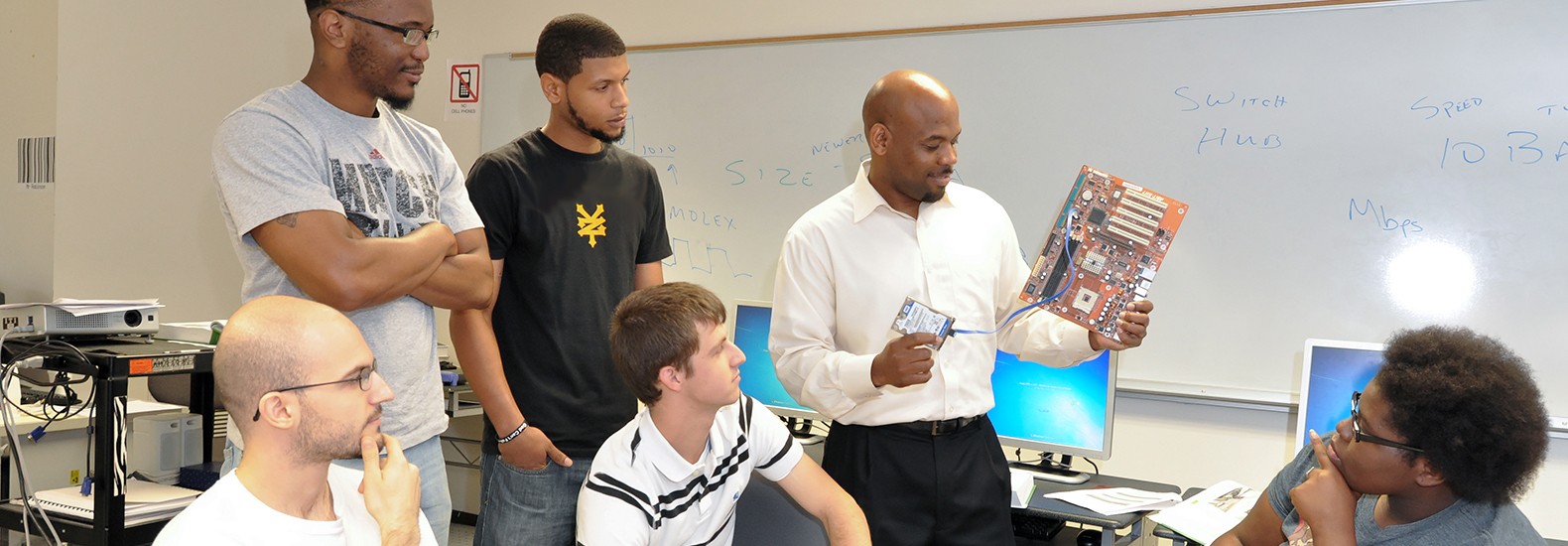
When you enroll in an information security school like ours there are a few things that you will immediately expect to learn. One thing that we do try to emphasize is real-world scenarios – when you graduate and leave the hallowed halls of our institution, there are definitely some very real scenarios that you are going to encounter, some of which are easier to solve than others. Today we’re going to talk about PCI compliance and what it means for information technology training.
PCI Compliance in Information Security School
When we talk about PCI compliance, we’re speaking of the Payment Card Industry Data Security Standard or PCI DSS. PCI compliance is a standard that applies to any company regardless of size so long as they accept credit card payments. If a company, for example, is intending to accept credit card payments, then it will need to host its data on a server that uses PCI-compliant technology. They can do this by themselves, so long as they meet all of the compliance standards, or they can hire the services of a hosting provider.
PCI Compliance Goals
Compliance has a number of goals that you should familiarize yourself with, but in the end, the primary goal is to create a secure network.
To ensure proper PCI compliance in-house, businesses must:
- * Install and Maintain Firewall Configuration that Protects Cardholder Data
- * Create Firewall Configuration Policy
- * Develop configuration Test Procedures
In most cases, hosting providers will already have firewalls in place that will protect and secure a private network, meaning it’s one step that you, as a professional will not have to worry about.
Say No to Vendor Defaults
 When you rent your first server for this purpose, you’re going to find that it is already secured with a password, which is great, now change it. One of the most important things you will learn in information security school is that default passwords are easily crackable whether the password is guessed or obtained using a brute force attack; in some cases, you might even have people who simply know what the password is. Did you know that for the longest time, most residential routers use the combination: of admin, and password for their login information? We wish that we were making that up, but it’s the absolute truth. To avoid snafus like this in the professional world, we strongly recommend that you change the passwords and create a few that are more secure. Cisco, for example, generates a root password before the servers are given to you.
When you rent your first server for this purpose, you’re going to find that it is already secured with a password, which is great, now change it. One of the most important things you will learn in information security school is that default passwords are easily crackable whether the password is guessed or obtained using a brute force attack; in some cases, you might even have people who simply know what the password is. Did you know that for the longest time, most residential routers use the combination: of admin, and password for their login information? We wish that we were making that up, but it’s the absolute truth. To avoid snafus like this in the professional world, we strongly recommend that you change the passwords and create a few that are more secure. Cisco, for example, generates a root password before the servers are given to you.
PCI compliance means securing on multiple levels. A combination of physical and virtual security methods is vital.
Virtual – Layers of Defense and Data Protection
Physics – Restricted Access to Server
Learn Encrypted Data at an Information Security School in Baton Rouge, LA
Transmission of data needs to be secure and should not be interceptable by a third party. It must be unreadable unless the individual receiving it has a cryptographic key. To put it simply, the data sent in the plain text must be scrambled, and when received, a cipher would be used to decrypt it – this process would be completed automatically.
Vulnerability Management
It is of vital importance to properly manage vulnerability in these programs. Some of the steps include:
- * Proper Firewall Deployment
- * Anti-Virus
- * Malware Scanning/Prevention
- * Auditing
Along with all of that, proper access control needs to be implemented which is something that you will learn all about in information technology school. We can provide you with the skills necessary to take part in the professional world and be a good, contributing member of any information technology team.
For more information about graduation rates, the median debt of students who completed the program, and other important information, please visit our website: https://iticollege.edu/disclosures/